
Information and Communication Security Policy
Information and Communication Security Policy
Version 1141021
Article 1 Purpose of Information and Communication Security Management
-
To ensure the security of Jia Jie Biomedical Co., Ltd. (the “Company”)’s servers, network equipment, and network communications; to effectively reduce the risks of information assets being stolen, misused, leaked, altered, or damaged due to human error, malicious acts, or natural disasters; and to establish information and communication security management standards.
-
To ensure the confidentiality, integrity, and availability of the Company’s business information.
※Confidentiality: Ensuring that information is accessible only to authorized personnel.
※Integrity: Ensuring that information used is accurate and has not been altered.
※Availability: Ensuring that authorized personnel can access required information when needed.
Article 2 Information and Communication Security Policy Content
-
All information and communication security management regulations of the Company shall comply with relevant government laws and regulations (such as the Cyber Security Management Act, the Criminal Code, the National Secrets Protection Act, the Fair Trade Act, the Multi-Level Marketing Supervision Act, the Trademark Act, the Copyright Act, and the Personal Data Protection Act, among others).
-
A dedicated information and communication security management unit shall be established and shall be responsible for the establishment and promotion of the information and communication security system.
-
Information and communication security education and training shall be conducted on a regular basis to promote the information and communication security policy and related implementation regulations.
-
Management mechanisms for the use of servers and networks shall be established to centrally allocate and utilize resources.
-
Prior to the deployment and operation of new systems and equipment, risks and security factors shall be taken into consideration to prevent situations that may compromise information and communication security.
-
Physical and environmental security protection measures for information facilities shall be established, and related maintenance and upkeep shall be carried out on a regular basis.
-
Authorization for the use of network systems shall be clearly defined to prevent unauthorized access.
-
An internal audit plan for the information and communication security management system shall be established. All personnel and equipment usage within the scope of the system shall be reviewed periodically, and corrective and preventive measures shall be formulated and implemented based on audit reports.
-
Business continuity management drills for backup and recovery shall be established to ensure the continuous operation of the Company’s business.
-
All personnel of the Company have the responsibility to maintain information and communication security and shall comply with the Company’s relevant information and communication security management regulations.
-
Where outsourced vendors require subcontracting in the course of performing outsourced services for the Company, the information security risks associated with such subcontracting shall be assessed. The Company shall also require outsourced vendors to appropriately supervise and manage subcontractors in accordance with relevant information and communication security regulations.
-
During the management of internal and external projects, all information and communication security requirements related to the projects shall be clearly specified and stated to ensure the confidentiality, integrity, and availability of internal and external project information, and to reduce the risks of sensitive information (including personal data) leakage and legal non-compliance.
-
The information and communication security policy shall be evaluated and reviewed at least once a year to reflect the latest developments in management policies, government regulations, new technologies, and the Company’s business operations, so as to ensure the feasibility and effectiveness of the information and communication security management system and to maintain operational continuity and the ability to provide appropriate services.
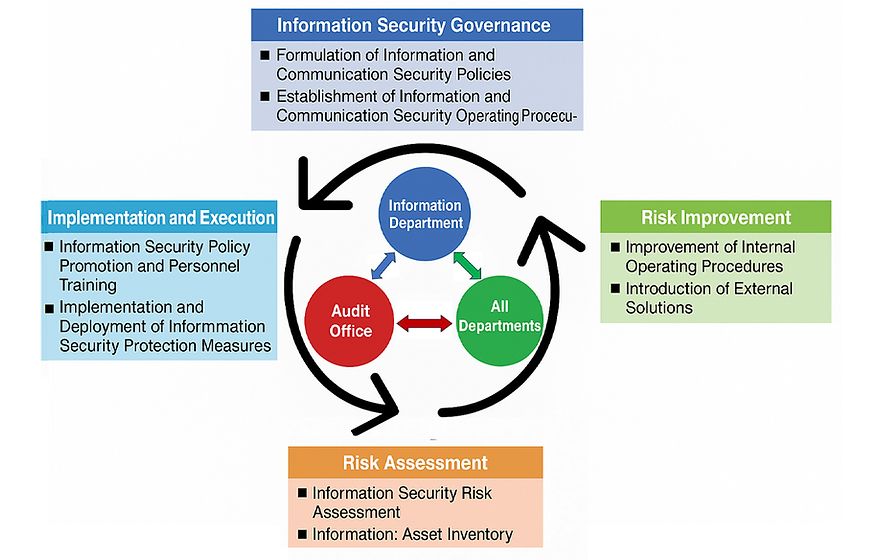
Article 3 Information and Communication Security Risk Management Framework
-
The Information Department is the responsible unit for information and communication security of the Company. The department is staffed with an information executive and professional information personnel, and is responsible for formulating internal information and communication security policies, planning and implementing security protection measures, promoting and enforcing security policies, and regularly disclosing the status of the Company’s information security governance.
-
The Audit Office serves as the supervisory unit for information and communication security. The office is staffed with an audit executive and dedicated audit personnel, and is responsible for supervising the implementation of internal information security measures. Where deficiencies are identified through audits, the audited units shall be promptly required to propose improvement plans and specific corrective actions, and the implementation results shall be tracked on a regular basis to reduce internal information security risks.
-
The organizational operating model adopts periodic audits and cyclical management to ensure the achievement of reliability objectives and continuous improvement.
Article 4 Specific Management Measures for the Information and Communication Security Policy
The Company’s information security management framework comprises the following four dimensions:
-
Formulation of Information Policies:
The Company establishes information security operating and management regulations to clearly define personnel conduct with respect to information operations.
-
Application of Information Technology:
The Company implements information security management facilities and continuously upgrades and replaces software and hardware information systems in order to align with current information security risk control requirements.
-
Information Security Awareness and Training:
The Company continuously conducts information security awareness programs and education and training for personnel to enhance overall information security awareness among all employees.
-
Information Security Auditing and Improvement:
The Company’s audit department regularly audits the information security function. Risk assessments are conducted through established risk assessment processes focusing on information security and network risks, and appropriate control recommendations are proposed. The information department makes adjustments and improvements accordingly.
The information and communication security policies and management measures implemented by the Company include the following:

Article 5 Information and Communication Security Incident Reporting Procedure

The Company’s information and communication security incident reporting procedure is as follows. All reporting and handling of information security incidents shall be conducted in strict compliance with the provisions of this procedure.
Execution status of the current year
Invest funds
項目project | 主要內容Main content | 經費(萬)Funding (in ten thousand) |
|---|---|---|
Datong Trend ApexOne Antivirus Software | Provides computer device virus protection and email filtering | 12.8 |
ISO 27001 recertification guidance and recertification fees | Assist in passing ISO 27001 certification | 100 |
Information security incident
資安指標Information security indicators | 資安客訴事件Cybersecurity customer complaint cases | 外部破壞、竊取資料或病毒威脅事件External sabotage, data theft, or virus threats | 資訊系統異常或設備異 常影響營運事件Information system malfunctions or equipment abnormalities affecting operations |
|---|---|---|---|
2025年事件統計 | 0件 | 0件 | 0件 |
